2.2 Encryption in wireless networking
This section is part of the amber and green pathways.
Since wireless networks transmit data over a medium that is shared by everyone, anyone with a compatible receiver or transceiver is able to eavesdrop on the radio signals being sent. It is somewhat similar to being able to ‘tune in’ to a radio station.
Ensuring that the eavesdropper is not able to convert these signals into the original message is a desirable security property of any wireless network, referred to as ensuring confidentiality. (This was one of the three security essentials we mentioned earlier, along with integrity and availability.)
Another security problem with using a shared medium for transmission is that malicious users could interpose themselves between a sender and a receiver and modify the messages being exchanged or even destroy them entirely. This is sometimes called a ‘man-in-the-middle attack’, and it compromises the integrity of the data being transmitted across the network.
Finally, an attacker could transmit lots of random data on the frequency being used by the wireless network, congesting the network and thus preventing other users from sending data. As we saw earlier in the course, this is called a ‘denial-of-service’ (DoS) attack and is an example of an attack on the availability of the network.
How encryption can help
So how do wireless networks address these potential security issues?
One commonly used security mechanism is encryption, which can help to ensure both the confidentiality and the integrity of data. The idea of encryption is to take the information you wish to protect and transform it into a different form, such that only the people who are supposed to receive the information are able to reverse the transformation and recover the original information. This is like having a key to unlock a door; only a person with the right key can open it.
Encryption can help ensure:
- Confidentiality – When a message is encrypted using a particular key, it can only be decrypted to recover the original information if the same key is used. This ensures that messages are confidential between the sender and the receiver.
- Integrity – Encryption can prevent messages from being modified without the receiver’s knowledge.
- Authentication – Encryption can contribute to the process of proving the identities of the sender and receiver.
You will look at encryption and decryption in more detail next week when we explain how cryptography works.
Encryption in Wi-Fi
Since Wi-Fi was first introduced, a number of security techniques have been used to protect Wi-Fi networks from unauthorised users and to ensure that the data transmitted across them is secure. The most common methods are based on encryption, using a key known only to the nodes in the wireless network.
The first of these mechanisms was called Wired Equivalent Privacy (WEP), which (as the name suggests) aimed to provide confidentiality comparable to that of a wired network. Since 2001, a number of serious problems have been identified in WEP that allow the encryption key to be computed within a few minutes, using readily available software. Many wireless devices still support WEP to ensure compatibility with older equipment such as old modems, but users should switch to a more modern form of encryption.
At time of writing (2020), the recommended security mechanism for Wi-Fi networks is Wi-Fi Protected Access 2 (WPA2), which uses a more secure key to encrypt the transmitted data. This security mechanism has become the default configuration for Wi-Fi networks, and must be supported by all Wi-Fi devices for them to be compliant with the 802.11 standard. WPA (or WPA1) was an initial standard which is now superseded and WPA2(AES), meaning WPA2 with AES encryption, is the current standard. TKIP was an earlier encryption protocol used and it is not considered secure anymore.
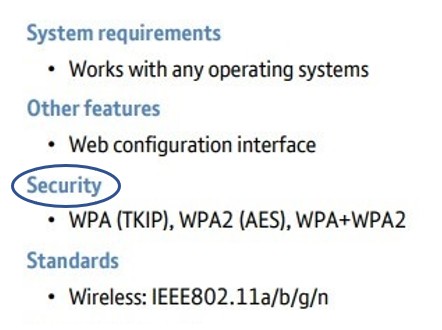
The snapshot of the Wi-Fi-enabled product specification from Section 1.4 is repeated below. Notice how the Wi-Fi security standards the product conforms to are specified. This product supports both versions of the WPA. You would choose to use WPA2(AES) only, unless you have older devices on your network supporting WPA(TKIP). In that case you would support both and choose to use WPA+WPA2 and plan to upgrade your existing WPA-only supporting devices to later versions that support WPA2.
In the next section you’ll consider how you might use Wi-Fi more securely.

