1 Identity theft
This section is part of the amber pathway.
Transcript
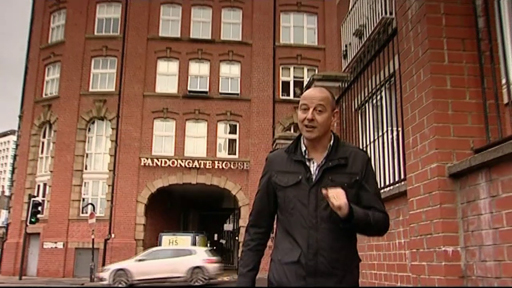
Identity theft is a type of fraud in which an attacker uses stolen personal information to impersonate another person. This video shows an extreme, though by no means unique, example of the possible consequences of identity theft for an individual.
Traditionally, this type of fraud was achieved by an attacker intercepting postal deliveries which contain personal information such as names, addresses, bank account details and so on. Attackers could then open credit card accounts and apply for loans in the victim’s name. Victims have had their financial security and lives ruined by identity theft.
The online world has opened up a new, lucrative source of information for fraudsters. Many users have been quite relaxed about sharing their information with online services and other users, but even security conscious individuals are threatened by malware designed to sniff out personal information on a computer, or phishing attacks that persuade users to divulge personal information. Additionally, as we have seen, hacking attacks on big retailers can make millions of personal records available for potential abuse.
Online identity theft is a major threat, especially to those who are new to online interactions. Online banking fraud cases have been increasing since 2013 and stood at 25,849 cases in 2019, amounting to £112 million (Statista, 2020a and 2020b).
Preventing identity theft
You can greatly limit your risk of online identity theft by following simple security procedures such as running an antivirus program, keeping it up to date and by not responding to phishing emails.
Detecting identity theft
Online identity theft may pass unnoticed for some time, during which great damage can be done to your financial security. Some signs that a victim might notice are:
- unexplained bank withdrawals or credit card charges
- bills and other expected official letters don’t arrive
- cards or cheques are declined
- debt collectors make contact about debts the victim knows nothing about
- they receive notice that their information was compromised by a data breach at a company where they do business or have an account
- their bank or credit card provider makes contact about suspicious behaviour on their account.
However, you cannot do much to prevent the loss of your details by other organisations that provide everything needed to steal your identity. In March 2020, Marriott announced that an unknown amount of guest information may have been accessed using the login credentials of two employees at a franchise property. The data of 5.2 million guests were compromised.
It is worth keeping an eye on your own free credit reports to make sure nothing unexpected is being shown that might indicate identity theft. In April 2020, 160,000 Nintendo (gaming platform) accounts were breached. Hackers had used the hijacked accounts to buy high value digital items.
Next, you’ll learn about what data loss can mean for organisations.
