3.2 Digital signatures and certificates
Transcript
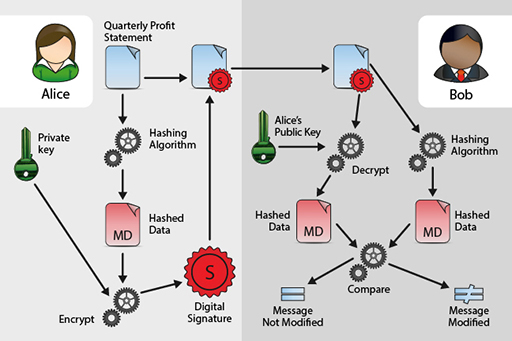
Hashing can show that data has not changed in transmission, but on its own cannot demonstrate that the data originated with its supposed author. To do that, a digital signature should be used.
Digital signatures use the sender’s private key to encrypt the hash. Previously, you learned how documents can be encrypted with a public key which can be used by anyone, but can only be decrypted using the corresponding private key known only to the owner.
Encrypting data using the private key isn’t suitable for securing secrets (as anyone with access to the public key could decrypt it). However, it is perfectly possible to encrypt a hash using the private key so that the hash can be decrypted and compared by anyone possessing the matching public key. This can be used to provide authenticity since the encrypted hash must have been produced by the holder of the private key – hence the name digital signature.
Case study 1: Alice and Bob
Imagine that Alice wants to send the company’s quarterly profit statement to Bob, who works in the financial markets, for public announcement. Both Alice and Bob want confidence that the quarterly profit statement has not been intercepted by Eve en route and altered.
Alice will therefore produce a hash of the quarterly profit statement and then encrypt this with her private key to produce a digital signature. Alice will then include the digital signature with the quarterly profit statement and send this to Bob. Alice may also encrypt the quarterly profit statement and the encrypted hash with Bob’s public key so that all details of the message remain secret.
Upon receipt Bob will, if Alice sent the message encrypted with his public key, decrypt the message using his own private key. This will then reveal the encrypted digital signature. He will decrypt the digital signature using Alice’s corresponding public key to reveal the hash. Bob will then calculate a hash of the quarterly profit statement and then compare this with the encrypted hash that he received from Alice. If the hashes are the same then both Bob and Alice can be confident that the quarterly profit statement was not altered en route by Eve.
Digital signatures do not provide us with complete confidence of the author or originator. Just because a digitally signed document claims to come from a person or a company it doesn’t mean that it actually did, a malicious individual could masquerade as the sender by producing their own public/private key pair and using these to produce digital signatures.
Case study 2: Alice and Bob
Imagine that a digitally signed business invoice arrives in Alice’s mailbox from Bob. She uses Bob’s public key from a public key server to decrypt the digital signature and validate the business invoice by comparing the hashes. Alice, assuring herself that it is Bob (as the hashes are the same), follows the instructions and transfers money to the account details in the business invoice.
A few weeks later, Alice receives an angry email from Bob because he has not been paid. After a bank investigation she finds out that she had transferred the money to Eve by mistake – so what went wrong?
It’s clear that the business invoice and the associated signature did not come from Bob, instead the signed business invoice actually came from Eve. Eve used Bob’s personal information to create a new key pair in Bob’s name and placed a copy of the public key on a public key server. Eve then used her corresponding private key to sign the business invoice and send it to Alice.
Alice, convinced that the document was a genuine business invoice from Bob (as it included what she believed to be his digital signature), followed the instructions and paid money into an account belonging to Eve – oh dear!
Digital certificates help us overcome this problem. A digital certificate is a means of binding public keys to their owner. These are issued by Certificate Authorities (CAs) who validate the owners of public keys. The CA does this by validating (through various processes), the identity of the owner of the public key. Once it has done this it will bind the public key to a digital certificate and sign it using its private key to attest authenticity. The CA’s public key is available to all parties who need to validate the CA’s assertion of public key ownership.
However, digital certificates still require a chain of trust to confirm that the certificate belongs to the person or organisation that you think it does and have not been compromised. Criminals have been known to obtain certificates that were then used to sign software that included malware. Stolen certificates have also been used to sign malware. For example, the Stuxnet code was signed with certificates that belonged to Realtek Semiconductor and JMicron Technology Corp.
Case study 3: Alice and Bob
So, using a Certificate Authority prevents Eve from creating a key pair of her own, and claiming that the corresponding public key is Bob’s. If Eve were to now send a business invoice appearing to be signed by Bob, when Alice uses Bob’s validated public key to try and decrypt the hash and compare them, this will not work; she would know that something was wrong, and (hopefully), not transfer money to Eve.
Note that scams are increasingly being reported where fake invoices are being sent to businesses, or a senior manager is being impersonated to persuade people in the business to make payments to the scammer’s account.
All businesses should ensure that all managers, directors etc. have private and public encryption keys, and that their public keys are stored and displayed locally to be used by everyone in the business.They must use their keys in order to sign and validate all non routine instructions for making payments. This is about the only way to avoid the scam reported by the BBC:
‘Hey, the deal is done. Please wire $8m to this account to finalise the acquisition ASAP. Needs to be done before the end of the day. Thanks.’
The employee thought nothing of it and sent the funds over, ticking it off his list of jobs before heading home.
But alarm bells started to ring when the company that was being acquired called to ask why it had not received the money.
An investigation began - $8m was most definitely sent, but where to?
For the rest of the report see: https://www.bbc.co.uk/ news/ technology-49857948 [Tip: hold Ctrl and click a link to open it in a new tab. (Hide tip)]