4.3.3 Security architecture
Securing IoE networks cannot be about securing just the individual devices. Rather, it is about implementing an end-to-end security solution.
A security solution that provides protection with centralised policy management and distributed enforcement must be integrated throughout the network. Continuous monitoring of activity on the network is needed to aggregate and correlate data across the connected environment, leveraging insights, and taking action as needed.
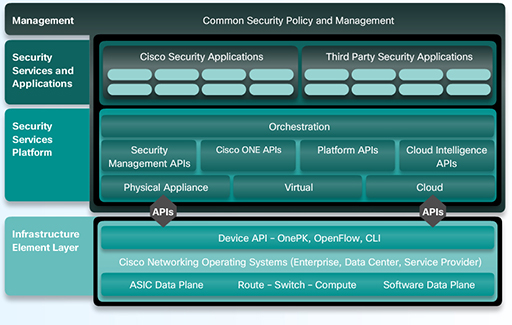
Cisco’s security architectures use infrastructure, platform, and application layers to provide a comprehensive set of tools and systems. These tools and systems work together to produce actionable security intelligence, in near real-time, while allowing the network to adjust to security threats with little or no human intervention required (Table 10).
| Access Control | Context-aware policies | Context-aware inspection and enforcement | Network and global intelligence |
| Access control provides policy-based access for any user or device seeking access to the distributed network. Users are authenticated and authorised. End devices are also analyzed to determine if they meet the security policy. Non-authenticating devices, such as printers, video cameras, sensors, and controllers are also automatically identified and inventoried. | Context-aware policies use a simplified descriptive business language to define security policies based on the full context of the situation: who is sending, what information, when, where and how. These security policies closely align with business policies and are simpler to administer across an organisation. They help businesses provide more effective security and meet compliance objectives with greater operational efficiency and control. | Context-aware inspection and security enforcement use network and global intelligence to make enforcement decisions across the network. Flexible deployment options, such as integrated security services, standalone appliances, or cloud-based security services bring protections closer to the user. | Network and global intelligence uses the correlation of global data to ensure that the network is aware of environments that have a reputation for malicious activity. It provides deep insights into network activity and threats for fast and accurate protection, and policy enforcement. |
Figure 11 shows a Cisco security architecture. The security principles described in the table above are applied across the layers of the architecture. The architecture includes the infrastructure layer at the bottom, which provides a set of application programming interfaces (APIs). These APIs deliver certain functions and applications to the security services platform layer above. At the top of the platform sits a common security policy and management layer that manages the entire platform.
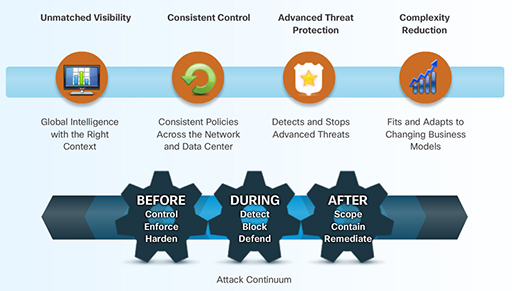
Implementing a Cisco security architecture provides the benefits shown in Figure 12, as well as continuous support before, during, and after a security event or attack.
Cisco is uniquely positioned in the IoE market. As a pioneer in the security industry, Cisco has end-to-end solutions within its product lines.