9.3 Firewalls – an overview
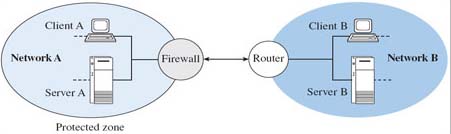
Firewalls play an important role in restricting and controlling access to networks. A firewall is normally implemented within a router or gateway, and will monitor incoming and outgoing traffic at the boundary of the protected zone. It is a device that denies external hosts access to selected insecure services within the protected zone (e.g. denial of dial-in services), while also denying internal hosts access to insecure services outside the protected zone. Figure 13 shows a firewall protecting the only access to network A. There may be further control within the protected zone, for example to limit access from one internal LAN segment to another. A firewall provides the means to implement some of an organisation's network security policies and may be transparent to users of the network in terms of its presence and the level of inconvenience caused. This depends on the type of firewall and the policies that are implemented.
Activity 17
In the previous section I found it useful to regard a password as a type of key that would allow legitimate users access to particular services. Would you consider a firewall to be another type of key?
Answer
A firewall also allows or bars access to services, but its role is more selective in that users may be allowed access to some services but barred from others. To that extent it may be helpful to consider a firewall as performing a gatekeeping role, i.e. allowing access to some but not others.
I shall now look at three different types of firewall – packet-filtering routers, application level gateways, and circuit level gateways – concluding with examples of firewall implementation.
