1.5 Taking stock of your information assets
Before you can take steps to protect your corner of cyberspace, you need to know what information you have that needs protection: your information assets.
Activity _unit2.1.2 Activity 2 Your information assets
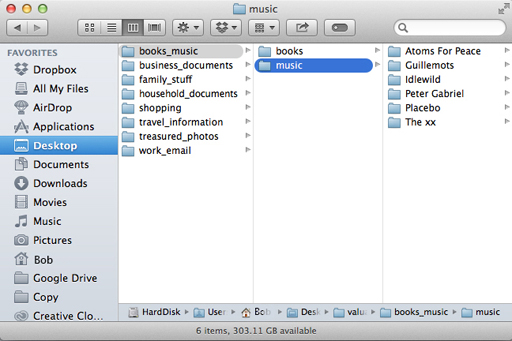
Compile a list, perhaps in a spreadsheet or using one of our templates, of the different types of information you store on your computer or online. For example, you may have personal correspondence, photographs, work documents or personal details such as your National Insurance number, insurance policy details and passwords for online services.
- Information assets list template (PDF) [Tip: hold Ctrl and click a link to open it in a new tab. (Hide tip)]
- Information assets list template (DOCX).
For each type of information, think of its value to you. Label the most valuable types of information as ‘High’, the least valuable as ‘Low’ and those that are in between as ‘Medium’.
The value could be the cost to replace the information, in time or money, or the impact of its loss on your reputation, for example, all your emails or photographs could all be published online.
Do the same exercise for the online activities you engage in. For example, you might use online banking, shopping or social networking services. This time, label each one with a value based on the potential cost of an unauthorised person gaining access to it.
In the next section, you will use this information as part of a survey that will help you get a picture of your exposure to information security threats but you won’t be asked to share the details of your list. You’ll use this list later in the course, too.