Week 3: Malware
Introduction

Transcript
The two biggest threats to consumers online are malware and phishing. Cory introduces you to malware (short for malicious software), which is the focus of this week.
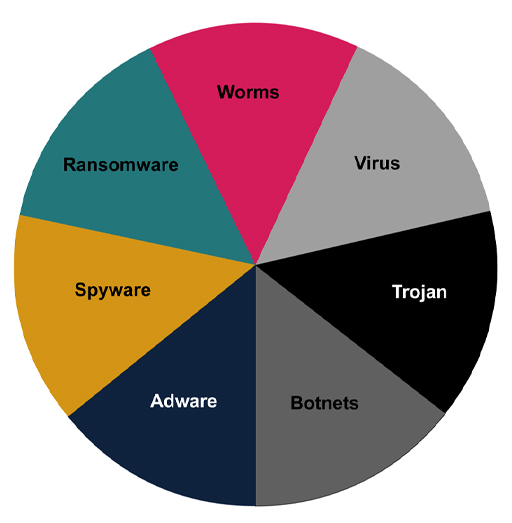
Malware is the collective name for software that has been designed to gain unauthorised access, and disrupt or damage data, software or hardware. There are several types of malware, such as viruses, worms and Trojans, which you’ll learn more about in the next few sections.
However, as malware has evolved from its beginnings as demonstrations of prowess by individual programmers to sophisticated technologies developed by organised crime, the boundaries between the different categories are beginning to blur. What is common though is the objective to obtain unauthorised access, with an intent to cause disruption or to steal information.
Week 3 game – Know Your Enemy
It is recommended that you use a desktop/laptop computer to play the games in this course, and use headphones where possible for the best audio experience.
Continue your learning by following the link to this week's game:
Week 3 game – Know Your Enemy (open this link in a new tab/window so you can come back here easily after playing the game) [Tip: hold Ctrl and click a link to open it in a new tab. (Hide tip)]
A note on learning pathways
Learning pathways are a recommendation only – you may choose to follow your own learning pathway and complete all sections, if you feel this will help you to complete the end of week quiz successfully.
Please note:
- The Amber pathway includes the extended topics of the week.
- The Green Pathway does NOT include the extended topics of the week.