1.1 Your own information assets
This section is part of the amber and green pathways.
In Week 1, you created a list of information assets that you possess. This was any sort of information that you store on a computer system that you use and which would be expensive, inconvenient, or impossible to replace if it was lost, damaged or stolen.
Spend a few minutes reviewing your list and thinking about whether you need to add anything based on what you have learned over the past eight weeks.
Lewis, a student of The Open University, did the same exercise on his own computers:
- study materials – documents and data relating to his postgraduate studies
- digital photographs – about 20,000 images taken over the last ten years
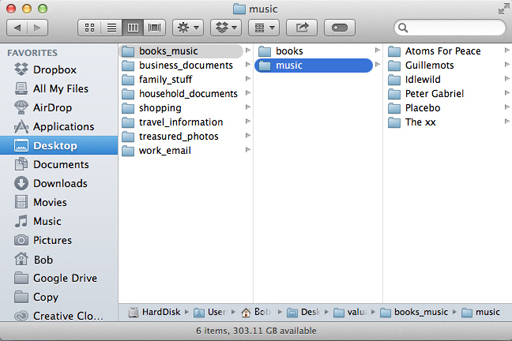
- music – about 10,000 tracks ripped from CD or bought online
- movies – about 200 films and TV programs
- email – about ten years worth of correspondence
- banking and other financial records
- passwords and account details.
Duplicates of some of these assets could be obtained if he lost the originals, for instance iTunes will allow him to download new copies of any lost music, but it would take a very long time to rebuild the entire library. Some others, such as emails and financial records could be recreated, but only by spending a lot of time asking for information from other people.
Passwords could be changed and other authentication information could be recovered, but again it would take a great deal of time and inconvenience to get back to normal. If these items had been stolen, an attacker might have been able to misuse those assets. The photos would, almost certainly, be lost forever.
Now look back at your own list of information assets. Does Lewis’s list prompt you to add any items to yours?
Next, you will learn about risk analysis.