Types of Cybercrime
Cybercrime takes many forms. Here are the most common types of cyber threats businesses need to be aware of—and which cybersecurity professionals can help combat.
1. Financial Cybercrime and Fraud
Financially motivated cybercrimes account for the largest share of attacks, targeting individuals, businesses, and financial institutions. These crimes have far-reaching consequences, often causing severe monetary losses, operational disruptions, and legal complications for affected organizations.
Business Email Compromise (BEC) is a major threat, with cybercriminals using social engineering to manipulate employees into transferring company funds or revealing sensitive information. In 2023 alone, BEC scams resulted in losses exceeding $2.9 billion (FBI IC3, 2023).
"BEC scams cause losses of over $2.9 Billion a year."
These attacks often target executives, financial officers, and payroll departments, leading to significant financial and reputational damage. For companies, falling victim to BEC fraud can mean disrupted operations, loss of stakeholder confidence, and even legal repercussions if customer or partner funds are misappropriated.
Identity theft is yet another costly cybercrime affecting businesses. Attackers gain access to employee or customer credentials, using them to commit fraud, steal funds, or manipulate financial records. Identity theft not only impacts individuals but also damages businesses that fail to protect personal data. Regulatory agencies impose steep penalties on organizations that do not secure customer information, making it a costly issue in both direct financial losses and compliance fines.
Businesses affected by financial cybercrime often struggle to recover, as losses extend beyond monetary damages to include reputational harm, legal battles, and loss of customer trust. The increasing sophistication of cybercriminals means that companies must implement strong security measures, employee training, and proactive fraud detection systems to protect their financial assets and maintain stability in an increasingly hostile digital environment.
2. Ransomware Attacks
Ransomware is one of the most devastating forms of cybercrime for businesses, as it not only disrupts operations but can also lead to massive financial and reputational losses.
When attackers encrypt a company's files or systems and demand payment for their release, organizations often find themselves in a difficult position, weighing the cost of paying the ransom against the potential loss of critical data.
In 2023 alone, reported ransomware-related losses in America exceeded $59.6 million, and the true financial impact is likely much higher when considering downtime, recovery costs, and reputational damage (FBI IC3, 2023).
Ransomware remains one of the most significant cybersecurity threats, with attacks occurring at an alarming rate each year. In 2021 alone, there were over 623.3 million ransomware attacks globally, a staggering 105% increase from 2020 (AAG, 2025).
Experts say the frequency of ransomware attacks is nearly doubling each year.
The FBI estimates ransomware attacks cost businesses over $1 Billion dollars a year.
"Ransomware attacks cost businesses over $1 Billion a year."
One of the most concerning developments is the rise of Ransomware-as-a-Service (RaaS), where cybercriminal groups like ALPHV (BlackCat) sell or rent out ransomware kits to less sophisticated attackers, effectively expanding the pool of potential perpetrators. This has made ransomware more accessible and widespread, significantly increasing the number of attacks on businesses of all sizes.
Large corporations are not the only targets—small and medium-sized businesses, hospitals, and even local governments have fallen victim due to weaker security defenses.
Critical infrastructure sectors, such as healthcare, energy, hospitality, and finance, are particularly vulnerable, with ransomware attacks having the potential to halt essential services. For instance, MGM Resorts experienced a massive ransomware attack in 2023 that resulted in $100 million in damages and losses, disrupting hotel bookings, financial transactions, and customer data access. In industries like healthcare, such attacks can put lives at risk by shutting down medical systems and delaying patient care.
"A single attack can cause hundreds of millions in losses."
Adding to the severity of ransomware threats, cybercriminals have evolved their tactics beyond simple encryption, employing double and triple extortion schemes. In these cases, attackers not only lock access to data but also threaten to sell or publicly release sensitive company or customer information if the ransom is not paid.
This places companies in a position where they risk both financial loss and severe reputational damage. A breached company may be forced to deal with lawsuits, regulatory penalties, and loss of customer trust, all of which can have long-term consequences for business viability.
For businesses, ransomware represents a multifaceted crisis that extends far beyond just the immediate loss of access to data. The time and resources required for recovery can cripple operations, especially for smaller businesses that lack the necessary cybersecurity infrastructure.
Some companies may even choose to pay the ransom in hopes of restoring access, but this does not guarantee that attackers will follow through, and it further emboldens cybercriminals to continue targeting businesses.
Given the escalating nature of ransomware threats, preventative measures such as robust backup strategies, employee training, endpoint protection, and rapid response planning are crucial.
Companies that fail to invest in cybersecurity risk severe operational disruptions, financial penalties, and reputational fallout that may take years to recover from.
The financial impact of ransomware is enormous. In 2021, the average ransomware payment rose 82% year-over-year, reaching a record-high $570,000 per incident (Palo Alto Networks, 2021).
Some high-profile attacks have seen ransom demands exceed $10 million, particularly against critical infrastructure, healthcare providers, and large enterprises.
However, the true cost of ransomware extends far beyond ransom payments, with organizations suffering from downtime, lost business, regulatory fines, and reputational damage.
Ransomware primarily spreads through phishing emails, unpatched vulnerabilities, and compromised credentials. Studies show that 41% of ransomware infections originate from phishing attacks, while 32% exploit unpatched security vulnerabilities in outdated software and systems (Palo Alto Networks, 2021).
Cybercriminal groups such as REvil, DarkSide, and Conti have been responsible for some of the most destructive ransomware campaigns in recent years, targeting businesses across industries, from manufacturing and finance to government agencies and healthcare providers.
Research indicates that 79% of organizations that pay the ransom still face additional extortion attempts or experience another attack within months.
Organizations that implement regular data backups, endpoint protection, cybersecurity, and employee training are better equipped to withstand ransomware attacks without paying the ransom.
As ransomware tactics continue to evolve, businesses and cybersecurity professionals must stay vigilant. Implementing zero-trust security frameworks, enforcing multi-factor authentication (MFA), and adopting proactive threat-hunting measures can significantly reduce the risk of ransomware infections.
With ransomware expected to become even more prevalent in the coming years, organizations that prioritize cybersecurity investments will be better positioned to mitigate this growing threat.
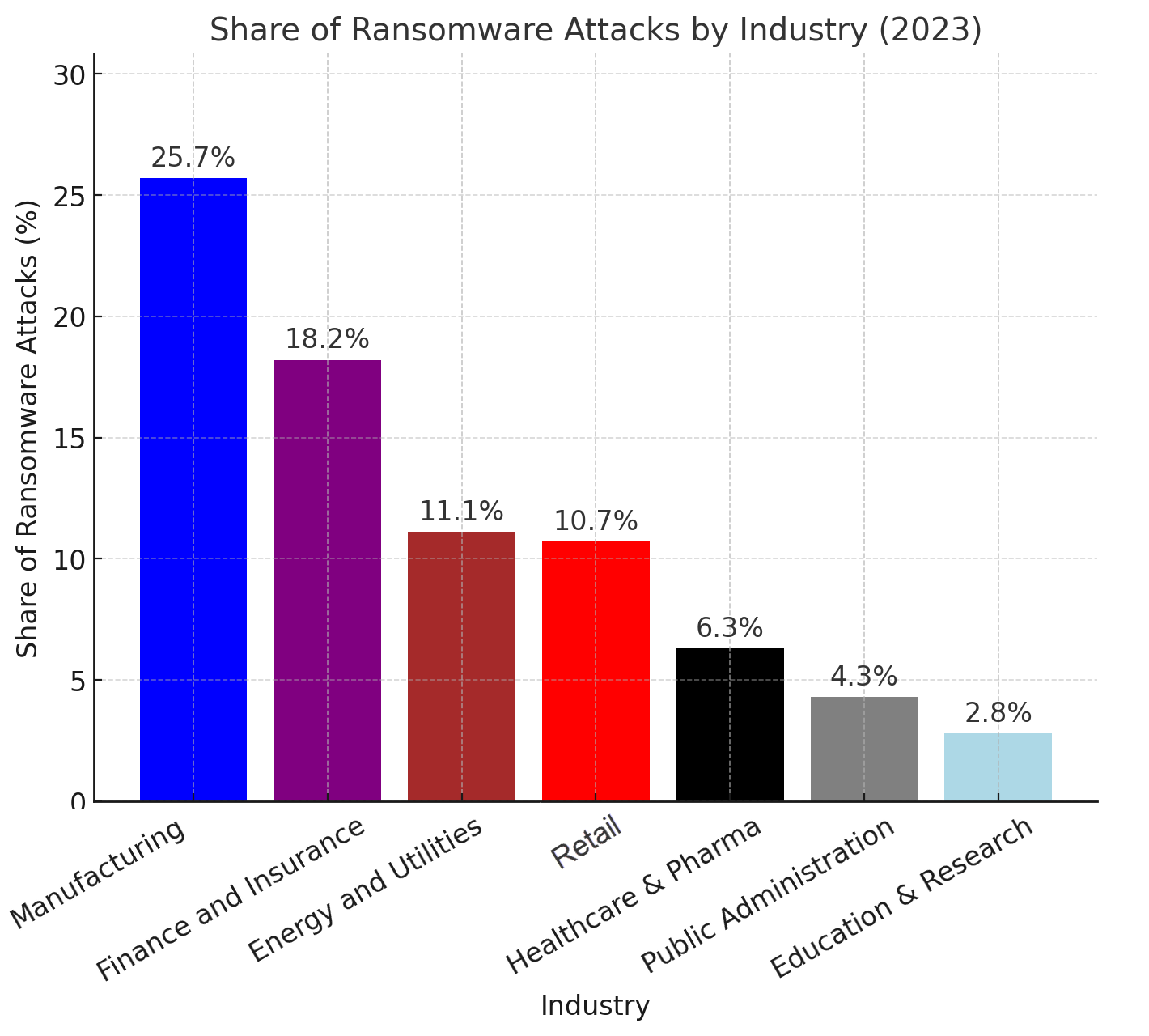
Image Description for Accessibility Purposes
A bar graph chart displays the following statistics about the share of ransomware attacks by industry: Manufacturing: 25.7%; Finance and Insurance: 18.2%; Energy and Utilities: 11.1%; Retail: 10.7%; Healthcare and Pharma: 6.3%; Public Administration: 4.3%; Education and Research: 2.8%.
3. Phishing and Social Engineering Attacks
Phishing and social engineering attacks represent one of the most persistent and damaging threats to businesses, with 298,878 reported cases in the US in 2023, making it the most prevalent form of cybercrime by a significant margin (FBI IC3, 2023).
Unlike traditional hacking techniques that exploit software vulnerabilities, phishing exploits human psychology, tricking employees into revealing sensitive information, clicking on malicious links, or executing fraudulent transactions. Attackers rely on deceptive emails, phone calls (vishing), text messages (smishing), and fraudulent websites (pharming) to impersonate legitimate entities and manipulate their victims.
For businesses, the consequences of phishing attacks can be severe. Employees who fall victim to phishing scams may inadvertently hand over login credentials, banking details, or proprietary company data, leading to financial fraud, identity theft, or unauthorized system access.
Attackers often use compromised accounts to escalate their attacks, moving laterally within a network to access more critical information or deploy malware, ransomware, or spyware undetected.
In many cases, phishing is the initial step in a larger cyberattack, making it one of the biggest entry points for data breaches.
The financial implications of phishing for businesses are staggering. Stolen credentials frequently lead to unauthorized wire transfers, fraudulent invoice payments, and unauthorized purchases, costing companies millions in direct losses.
"Phishing scams can cost businesses millions in losses."
Additionally, phishing often results in regulatory fines and compliance violations, particularly when customer data is exposed due to a breach. Under regulations such as GDPR, HIPAA, and CCPA, businesses are legally required to safeguard customer information, and failure to do so can lead to steep financial penalties and lawsuits.
Beyond financial losses, phishing attacks can cause long-term reputational damage. When a company suffers a data breach due to phishing, customers and stakeholders lose trust, leading to declining sales, customer churn, and reduced investor confidence.
High-profile phishing incidents, such as those affecting banks, tech firms, and healthcare organizations, make headlines and tarnish the credibility of affected companies, sometimes leading to long-term brand damage.
One of the most concerning aspects of phishing is its evolution and increasing sophistication. Cybercriminals now use AI-generated emails that are nearly indistinguishable from legitimate communications.
Spear phishing targets specific employees, often executives or financial officers, using personal details to craft convincing scams.
Business Email Compromise (BEC) schemes, where attackers impersonate CEOs or vendors to authorize fraudulent wire transfers, have cost businesses billions of dollars annually.
As phishing attacks grow more advanced, cybersecurity professionals play a crucial role in helping businesses defend against them.
Companies must implement email filtering solutions, multi-factor authentication (MFA), regular employee training, and phishing simulation exercises to strengthen their defenses.
Cybersecurity freelancers and consultants specializing in phishing prevention are increasingly in demand, as businesses recognize the need for proactive strategies to protect against these highly deceptive attacks.
4. Data Breaches and Corporate Espionage
Data breaches and corporate espionage have become some of the most significant threats to businesses, causing severe financial losses, reputational damage, and regulatory scrutiny.
The global average cost of a data breach in 2024 reached $4.88 million, representing a 10% increase from the previous year (IBM, 2024). The financial impact extends beyond direct losses, as affected companies often face regulatory fines, legal settlements, and long-term brand damage, making breach prevention a top priority.
One of the primary causes of data breaches is insider threats, which can be both intentional and accidental.Employees with misconfigured access rights, weak security practices, or malicious intent pose a significant risk to organizations.In some cases, disgruntled employees may leak sensitive company information, while in others, well-meaning staff may inadvertently expose confidential data due to phishing attacks or poor password hygiene. Insider threats are particularly dangerous because they bypass traditional security measures, making them harder to detect and prevent.
Another growing concern is shadow data, referring to unmonitored and unstructured data that companies fail to track properly.
In 2024, 1 in 3 breaches involved shadow data, making it increasingly difficult for organizations to safeguard sensitive information (IBM, 2024). Shadow data often exists outside of controlled environments, such as on personal cloud storage, external hard drives, or unprotected internal servers.
Companies that do not implement strict data governance policies and real-time monitoring find themselves at higher risk of breaches caused by misplaced or unsecured data.
The shift to cloud computing has also introduced new vulnerabilities, with 82% of breaches occurring in cloud environments (IBM, 2024).
Businesses increasingly rely on cloud-based services for storage, collaboration, and remote work, but many fail to properly configure security settings, enforce multi-factor authentication, or implement data encryption.
Cybercriminals exploit weak security policies to gain access to sensitive information, often by leveraging stolen credentials, misconfigured permissions, or exploiting API vulnerabilities.
Breaches spanning multiple cloud environments have proven to be even costlier (IBM, 2024).
Beyond financial losses, corporate espionage has become a growing concern, particularly for companies operating in highly competitive industries such as technology, finance, and defense.
State-sponsored actors and private hacking groups target intellectual property, trade secrets, and proprietary research, often with the goal of gaining a competitive edge or influencing geopolitical outcomes.
In many cases, these attackers infiltrate organizations through sophisticated phishing campaigns or malware implants, maintaining persistent access for extended periods before being detected.
Businesses that suffer data breaches or espionage attacks often struggle to recover, as competitors may gain access to proprietary designs, patented technologies, or confidential business strategies.
The financial fallout extends beyond immediate incident response costs, as companies must rebuild customer trust, reinforce security infrastructure, and navigate potential lawsuits or regulatory investigations.
To mitigate these risks, businesses must adopt comprehensive security strategies, including advanced threat detection, regular security audits, and strict data access controls. Investing in cybersecurity training for employees and enforcing robust cloud security policies can significantly reduce the likelihood of a breach.
Organizations that fail to take proactive measures, however, risk falling victim to costly data leaks, intellectual property theft, and irreversible reputational harm in an increasingly digital world.
5. Cyber Warfare and Nation-State Attacks
Cyber warfare and nation-state attacks pose a unique and severe threat to businesses, government agencies, and critical infrastructure.
These attacks differ from traditional cybercrimes because they are often carried out by well-funded groups affiliated with national governments, using advanced persistent threats (APTs) and highly sophisticated hacking techniques.
Unlike financially motivated cybercriminals, state-sponsored attackers often aim to disrupt economies, steal intellectual property, conduct espionage, or weaken geopolitical rivals.
One of the most significant concerns in recent years has been large-scale supply chain attacks, which target not just a single organization but entire industries and government systems. These attacks compromise software providers or cloud services to inject malware or gain unauthorized access to sensitive systems.
The SolarWinds attack in 2020 was one of the most devastating supply chain breaches, affecting U.S. federal agencies, Fortune 500 companies, and critical infrastructure operators worldwide.
Government entities were among the primary victims, underscoring the importance of robust cybersecurity strategies for public sector organizations.
"The SolarWinds attack caused a national state of emergency."
Another emerging trend is AI-driven cyber warfare, where nations use machine learning and artificial intelligence to automate cyberattacks, identify vulnerabilities faster than human analysts, and conduct disinformation campaigns.
AI is being used to generate sophisticated phishing attacks, create realistic deepfakes for social engineering, and automate penetration testing tools that can infiltrate government and corporate networks at an unprecedented scale.
Governments must invest heavily in AI-powered cybersecurity defense mechanisms to counter these evolving threats.
For cybersecurity professionals and freelancers, working with government agencies presents a highly specialized and lucrative niche.
Governments increasingly rely on private contractors and cybersecurity consultants to help fortify national infrastructure, secure classified information, and defend against sophisticated adversaries.
Freelancers specializing in penetration testing, vulnerability assessments, digital forensics, and incident response can find opportunities to work with defense contractors, intelligence agencies, and government-backed cybersecurity initiatives.
Businesses, particularly those in energy, defense, finance, and healthcare, also face heightened risks from nation-state-sponsored cyber espionage. Chinese, Russian, Iranian, and North Korean hacking groups have been linked to theft of trade secrets, intellectual property, and proprietary technologies, particularly targeting industries critical to national security.
Corporations must adopt military-grade cybersecurity protocols, including zero-trust architectures, air-gapped systems, and continuous threat intelligence monitoring, to protect against these threats.
The rise in cyber warfare means that both government agencies and private-sector organizations must shift from a reactive to a proactive security approach.
Defensive strategies must now include cyber threat intelligence, red teaming exercises, real-time monitoring, and rapid response frameworks to detect and neutralize threats before they cause significant harm.
With geopolitical tensions escalating worldwide, cybersecurity professionals who can safeguard against nation-state attacks, cyber espionage, and infrastructure sabotage will be in high demand across both public and private sectors.
- Business Email Compromise (BEC) scams caused $2.9B in losses in 2023
- Ransomware attacks exceeded 623.3M globally in 2021, doubling yearly
- 79% of companies that pay ransomware face repeat attacks
- Phishing was the top cybercrime in 2023, with 298,878 reported cases
- Average cost of a data breach in 2024 reached $4.88M
- Nation-state cyber warfare targets businesses, infrastructure & governments
Palo Alto Networks. (2021). 2021 Unit 42 ransomware threat report. Unit 42. https://unit42.paloaltonetworks.com/ransomware-threat-report-highlights/
FBI IC3. (2023). 2023 Internet Crime Report. Retrieved from https://www.ic3.gov/AnnualReport/Reports/2023_ic3report.pdf
IBM. (2024). Cost of a Data Breach Report. Retrieved from https://www.ibm.com/reports/data-breach
Wollerton, M. (2023). Ransomware Attacks. https://doi.org/10.4135/cqresrre20230818.
